Quantum computing is rapidly advancing, challenging enterprise security strategies to evolve just as quickly. This change prompts a critical question: Do you know what cryptography your business depends on today?
Most organizations cannot fully answer this question. Quantum-computation methods pose a threat to today’s asymmetric cryptography, and new regulations, such as NIST’s PQC guidance, now require stronger systems. Discovering, analyzing, and planning for cryptographic changes is essential.
Additionally, with the latest release of IBM Quantum Safe Explorer, clients running Z-Linux platforms, including IBM Linux, can now use it via the command line interface (CLI). This update delivers Quantum Safe visibility directly to mission-critical workloads, seamlessly extending these capabilities.
Meet IBM Quantum Safe Explorer.
IBM Quantum Safe Explorer enables developers and security teams to quickly pinpoint cryptographic elements in application code, APIs, and environments. This utility streamlines cryptographic inventory and assessment for evaluating quantum readiness.
The tool helps track cryptographic assets, such as algorithms, keys, certificates, and libraries, across applications and infrastructure. It can generate cryptographic bills of materials (CBOMs) and assess cryptographic risks to prepare for quantum-safe transitions.
Security and compliance professionals can use the tool to answer critical questions about quantum readiness.
- Users can identify which cryptographic algorithms are deployed.
- Assess whether they are outdated or insecure.
- Locate where these algorithms reside.
- Determine which applications use them and evaluate preparedness to adopt post-quantum solutions.
With these new capabilities, clients using Z Linux and Linux One environments gain targeted answers to previously unresolved cryptographic questions, directly aligning with Quantum Safe Explorer’s core value.
Unlocking Crypto Agility with IBM Quantum Safe Explorer
Preparing for a quantum-safe future requires more than technical vulnerability scans. Organizations need visibility, agility, and management over encryption systems. IBM Quantum Safe Explorer supports diverse stakeholders, positioning CBOIMs at the center of risk management and long-term crypto-agility goals.
Value Delivered At Two Levels
- For InfoSec and DevSecOps Leads: Portfolio Visibility & Governance
Security and development leads gain clear visibility into cryptographic risks across portfolios. CBs provide a unified inventory for audits and compliance, highlight high-risk areas, and automate inventory generation in each development cycle for continuous oversight.
Dashboards display essential metrics, including new crypto components, changing risk scores, and remediation coverage across projects. This helps DevSecOps teams add cryptographic checks to the CI/CD pipeline with little disruption.
- For Leadership & the C-suite, translating risk into action
Executive dashboards distill technical details into clear business insights. Leaders quickly understand which applications depend on vulnerable cryptography, the completeness of cryptographic inventories, and areas needing agility improvements. Quantum Safe Explorer equips executives with compliance-ready evidence to demonstrate NIST quantum-safe conformance to regulators, supporting both current mandates and future requirements, such as the U.S. federal mandate for a cryptographic inventory by 2025. This enables leadership to prioritize risk mitigation and facilitate strategic planning for crypto agility investments.
This shift allows leadership to proactively manage cryptographic risk at the business level, ensuring strategic alignment and operational readiness for evolving security requirements.
Crypto Agility Anti-Patterns: What to Watch For
Crypto agility requires the ability to update cryptographic algorithms across systems efficiently and reliably. Quantum Safe Explorer identifies any practices that may hinder this flexibility, including embedded algorithm versions, absent fallback mechanisms, or inconsistent library implementations.
By identifying and mapping these issues to code paths, our solution provides teams with a clear plan for fixing them. This supports both current compliance and future resilience.
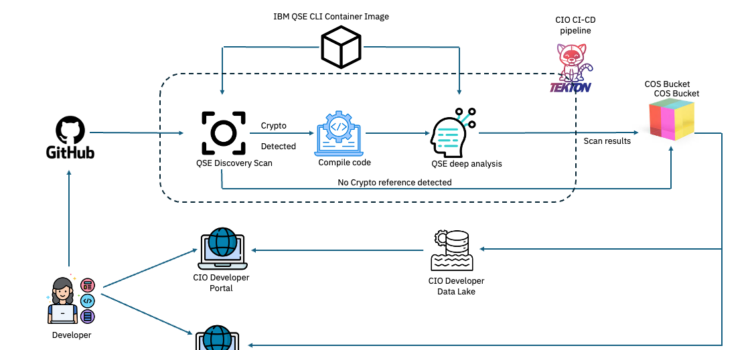
New CLI support for Quantum Safe Explorer on Z Linux.
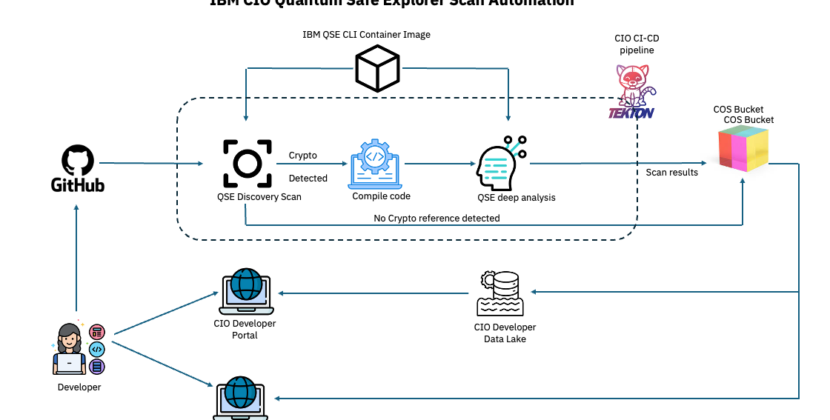
This release adds CLI support for zLinux, making it easy to integrate into secure environments such as financial systems, public cloud platforms, and other regulated workloads.
This means clients can now:
- Run cryptography discovery natively on Z Linux without moving data off the platform.
- Integrate QSE into CI/CD pipelines or system automation scripts.
- Generate CBOMs on demand for audit compliance or quantum readiness planning.
- Build a roadmap for replacing vulnerable cryptographic components over time.
The CLI was designed for Enterprise DevOps teams to get started: install it on zLinux and configure the required access credentials. Add CLI commands to existing process scripts or automation workflows to perform cryptographic discovery. Generate CBO and reports, and track assets. Run these steps at defined intervals or during build and deployment stages to ensure up-to-date visibility.
Why IBM LinuxOne 5?
IBM Linux One 5 provides a secure platform for IBM Quantum Safe Explorer, allowing firms to prepare applications for the future with post-quantum cryptography.
The system uses secure boot technology to prevent malware from being loaded during startup, improving cyber resiliency, and keeping the system safe. The crypto express 8s (CEX8s) hardware security module supports both classical and quantum-safe cryptography, meeting needs for confidentiality, integrity, and non-repudiation.
LIDEX One 5 protects sensitive data both when stored and in use, thanks to its cybersecurity and privacy features. Its built-in crypto accelerators, confidential computing, and NIST-standardized post-quantum cryptography provide a strong foundation for quantum resistance in modern IT systems.
Integration That Delivers: Security, Compliance, And Agility
Combining IBM Quantum Safe Explorer with IBM LinuxOne 5 brings multiple technical benefits, such as:
- Quantum Safe Explorer leverages LinuxOne 5’s crypto accelerators and confidential computing, enabling deep cryptographic analysis and protecting sensitive data throughout its lifecycle.
- Simplified compliance: the combined solution makes it easier to comply with regulations such as PCI DSS, FIPS, GDPR, and the EU’s Digital Operations Resilience Act (DORA).
What does this mean for LinuxOne clients?
IBM LinuxOne clients are familiar with security and availability. These systems are built to process sensitive workloads with built-in encryption, hardware isolation, and high availability.
However, even the most secure systems use cryptographic algorithms that may be decades old, and some of them are now at risk due to quantum computing. Many organizations also do not know where or how these algorithms are used.
With this release, LinuxOne clients can now perform cryptographic discovery directly on the platform without exposing data. They can identify algorithm dependencies early, enabling crypto agility before major changes are necessary. This also helps them prepare for new NIST post-quantum standards.
The solution makes it easier to meet compliance requirements for regulations such as FIPS, GDPR, and PCI DSS, which now require greater insight and control over cryptographic assets.
To summarize, Quantum Safe Explorer on Z-Linux helps organizations improve their cryptography practices and plan for the future directly within their LinuxOne environments, securely, efficiently, and at scale.