Today, Microsoft released its March 2026 Patch Tuesday updates addressing 79 security flaws. This includes two zero-day vulnerabilities that have been publicly disclosed.
Transitioning from the initial overview, Dispatch Tuesday also fixes three serious vulnerabilities. Two are remote code execution issues, and one is an information disclosure flaw.
Here is a breakdown of the number of bugs in each vulnerability category. In cybersecurity, a vulnerability is a weakness that could allow unauthorized actions in a system.
- 46 elevation of privilege vulnerabilities.
- Two security features bypass vulnerabilities
- Eighteen, remote code execution on the line of notice.
- Information Disclosure Vulnerabilities
- Four denial-of-service vulnerabilities.
- Four spoofing vulnerabilities.
Bleeping Computer only counts Patch Tuesday security updates released by Microsoft on the day itself. This means the total does not include 9 Microsoft Edge flaws or issues in Marina Payment Orchestrator Service, Azure, and Microsoft Devices Pricing Program that were fixed earlier this month. Thank you.
Two Zero-Day Vulnerabilities and Microsoft Office Flaws
This month’s Patch Tuesday addresses two publicly disclosed zero-day vulnerabilities with no reports of active exploitation.
Microsoft defines a zero-day flaw as one that is either publicly disclosed or actively exploited before an official fix is available.
The two publicly disclosed zero-day vulnerabilities are:
CVE-2026-21262 – SQL Server Elevation of Privilege Vulnerability
Microsoft has fixed this publicly disclosed SQL Server flaw.
Improper access control in SQL Server allows an authorized attacker to elevate their privileges on a network, Microsoft explains.
Microsoft credited Erland Sommarskog for discovering this flaw. He told Bleeping Computer that it was first disclosed in the “Packaging Permissions in Stored Procedures” article.
CVE-2026-2612. net denial of service vulnerability.
An “Out of bounds read” in .NET allows an unauthorized attacker to deny service over a network, Microsoft explains.
An anonymous researcher is credited with finding this flaw.
Microsoft has also addressed two remote code execution bugs (CVE-2026-26110 and CVE-2026-26113) in Microsoft Office. Remote code execution (RCE) refers to bugs that could allow attackers to run programs on your computer from a distance. These can be exploited through the preview pane, so users should update the application as soon as possible.
One remarkable issue is the Microsoft Excel Information Disclosure flaw (CVE-2026-26144), which could allow attackers to steal data using Microsoft Copilot. An information disclosure occurs when unauthorized people can access confidential data.
An attacker who successfully exploited this vulnerability could cause Copilot Agent Mode to exfiltrate data via unintended network egress, enabling a zero-click information disclosure attack, Microsoft explains.
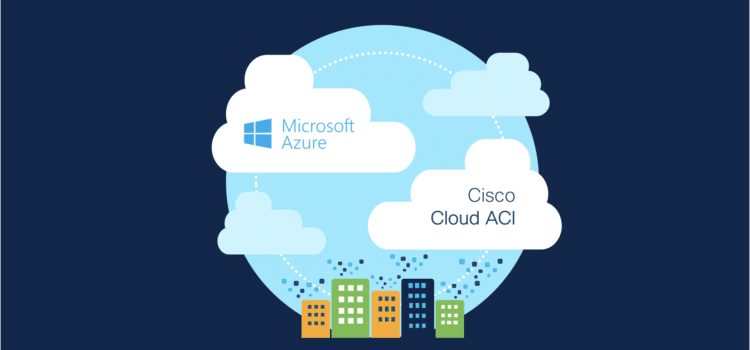
Turning to Azure Cloud Services, Microsoft has also fixed a vulnerability in Azure Container Instances (ACI) that could have allowed users to access information belonging to other Azure customers.
Microsoft did not share technical details about the vulnerability. However, Palo Alto Networks researchers say attackers could have used the bug to run code on other users’ containers, steal sensitive data like crypto secrets, or even install crypto-mining malware.
Microsoft said it notified customers who might have been affected through service health notifications in the Azure portal. The company added that anyone who did not receive a notification does not need to take any action.
There is no indication that any customer data was accessed as a result of this vulnerability. Out of an abundance of caution, Microsoft sent notifications to customers potentially affected by the researcher’s activities, advising them to revoke any privileged credentials deployed to the platform before August 31, 2021, Microsoft said in a statement.
Microsoft recommends that all Azure customers regularly rotate their privileged credentials as a precaution. Credential rotation involves frequently changing passwords or secure keys to reduce the risk of theft.
Palo Alto Networks researchers say the issue known as Azure escape could allow attackers to compromise Kubernetes clusters that host ACI. This would give them full control over other Azure customers’ containers.
ACI was designed to prevent attacks from malicious neighboring containers, such as cross-account or cross-tenant attacks. However, it used an older version of runc (the standard container runtime), which was vulnerable to several container escape flaws.
The researchers used a modified proof-of-concept code for CVE-2019-5736 to escape from a container and establish a root reverse shell on the host system. They then found token permissions in the Kube system namespace that allowed them to run commands on any pod in the cluster and carry out the cross-account attack.
A malicious Azure user could have compromised the multi-tenant Kubernetes cluster hosting ACI. As a cluster administrator, an attacker could execute commands in other customers’ containers, exfiltrate secrets and private images deployed to the platform, or deploy crypto miners. A sophisticated adversary would further investigate the detection protocols protecting ACI to avoid detection, Palo Alto said.
ACI, launched in July 2017, is a container-as-a-service (CaaS) that runs on multi-tenant clusters such as Kubernetes and Service Fabric. It lets users deploy containers without managing the underlying infrastructure.
In a related development, two weeks ago, Microsoft fixed a similar problem in Azure Cosmos DB. In that case, users could access other customers’ databases with full administrative rights, potentially gaining full control of them.
Source: Microsoft March 2026 Patch Tuesday fixes 2 zero-days, 79 flaws
Microsoft Warns of Information Leak Flaw in Azure Container Instances