Seattle, Wash.: A single data breach now costs large enterprises an average of $4.8 million. This staggering figure forces chief information security officers to rethink their approach to cloud infrastructure security. When organizations process highly sensitive data, securing the perimeter is no longer sufficient. The recent introduction of the Nitro Isolation engine highlights exactly how AWS Nitro security changes impact US cloud pricing for organizations across the financial and healthcare sectors. To maintain strong cloud infrastructure security, enterprise architects must navigate a new pricing landscape driven by advanced AWS Nitro security innovations. As workloads grow in complexity, financial planning necessitates a thorough comprehension of these operational expenses.
The Economics of Hardware-Enforced Isolation
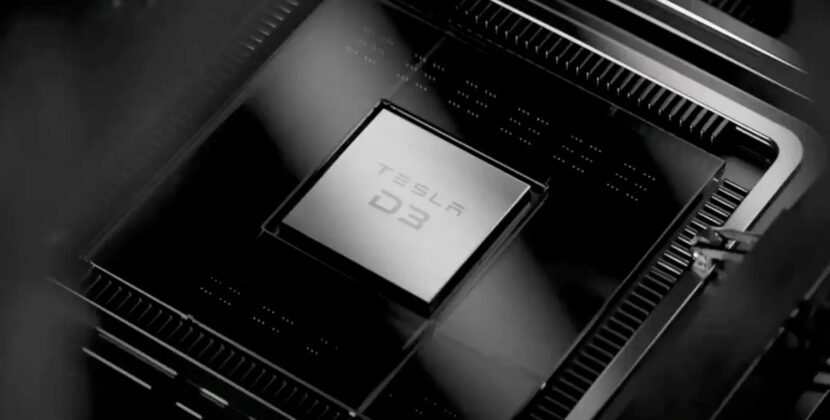
Moving to hardware-level isolation means companies need to invest more up front. AWS uses a separate Nitro chip to keep workloads isolated. This setup stops even privileged host operating systems from accessing memory. For organizations with tight data isolation rules, this brings peace of mind. However, keeping cloud computing this secure comes at a higher cost.
Organizations using multi-tenant models see higher cloud costs when they switch to Nitro-based enclaves. Standard EC2 instances handle unencrypted workloads, but confidential computing needs special instance sizes and costs more per hour. These expenses add up as companies run detailed workflows through different networks.
Take a large retail bank that processes credit card transactions. The bank needs to use isolated enclaves for its payment validation algorithms. This extra layer of isolation increases the monthly computing bill by about 20%. The added cost comes from the special hardware needed to keep memory separate.
Managing Regulatory Standards And Pricing
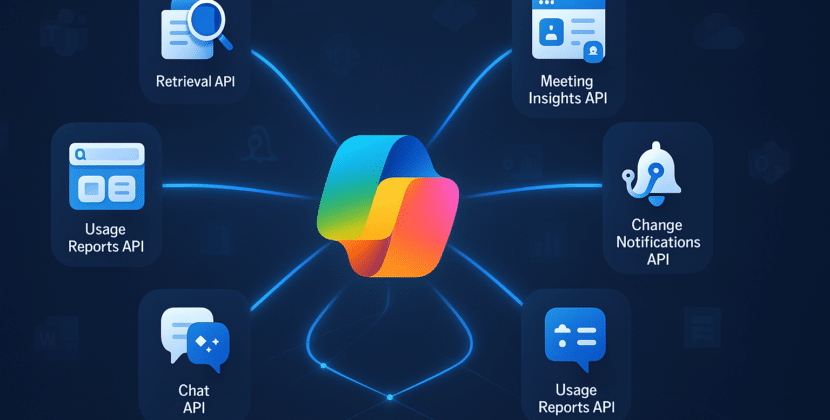
Dealing with AWS compliance rules is challenging for IT departments. Healthcare providers and financial institutions must follow strict guidelines for handling sensitive customer data. Using a dedicated AI security cloud layer helps keep model weights and training data safe during use. To meet AWS compliance, companies often have to choose more expensive instance types when setting up these secure enclaves.
Consider a major wealth management firm training large language models on personal financial data. The firm must utilize an AI security cloud configuration that employs cryptographic attestation. This process increases the operational budget for secure cloud computing by nearly 30% compared to standard cloud hosting.
The higher costs come from the hardware limits of running enclave applications. When a workload runs in an enclave, it cannot use the full resources of the parent instance. This means companies need to set up more instances to handle the same amount of work. As a result, system architects have to rethink their capacity plans. This leads to higher resource spending.
Market Dynamics And Enterprise Budgets
The transition towards hardware-level attestation changes the financial forecast for cloud architecture. Cloud providers have historically competed on raw CPU performance and adaptable pricing models. Now, the baseline includes hardware-enforced cloud infrastructure security. This evolution alters chief technology officers’ procurement strategies nationwide.
When calculating total enterprise cloud costs, finance teams must include specialized enclaves and encryption keys as a standard. A thousand-node cluster dedicated to internal data processing experiences a 25% increase in baseline computing costs when migrating to Nitro isolated instances. These higher fees reflect the additional hardware checks dedicated to data protection.
Also, the Nitro isolation engine employs formal mathematical checks to ensure data cannot be accessed by other tenants. This setup limits the amount of cache memory that can be shared between virtual machines. As a result, companies lose some of the efficiency benefits of traditional multi-tenant systems. This trade-off between efficiency and protection is the key to the change in pricing. The new AWS Nitro security features are changing how companies plan their cloud budgets.
Optimizing Budgets Under New Constraints
Technology leaders need to reduce these additional costs without weakening security. One way is to use isolated enclaves only where they are most needed. Instead of putting all microservices in enclaves, teams can isolate just the payment processing and sensitive personal data. This precise approach helps keep operating expenses under control.
Another way to save is to use an extended savings plan for Nitro-based instances. By agreeing to use these instances for 1 or 3 years, organizations can cut their hourly rates by up to 35%. This discount helps balance out the higher costs of confidential computing.
Forward-thinking organizations also use monitoring tools to make sure their instances are the right size. By checking CPU and memory usage, IT teams can reduce overly large enclaves and reallocate resources to where they are needed most.
Future Horizons
Adding hardware-level isolation is a lasting change in how cloud architecture is priced. Companies that update their systems without careful planning could see their profit margins shrink. The key measure for large hardware investments is the ability to scale clusters while keeping costs steady.
Source: AWS Blogs