Redmond, WA.: a federal contract is paused due to one key issue: being ready for cryptography needs after 2030. The challenge is not about cost or performance, but meeting compliance standards. For Microsoft, this means Azure security must review identity systems built over the last ten years. NIST compliance is now a firm requirement in procurement, not simply a suggestion.
The Compliance Trigger Behind Identity Overhaul.
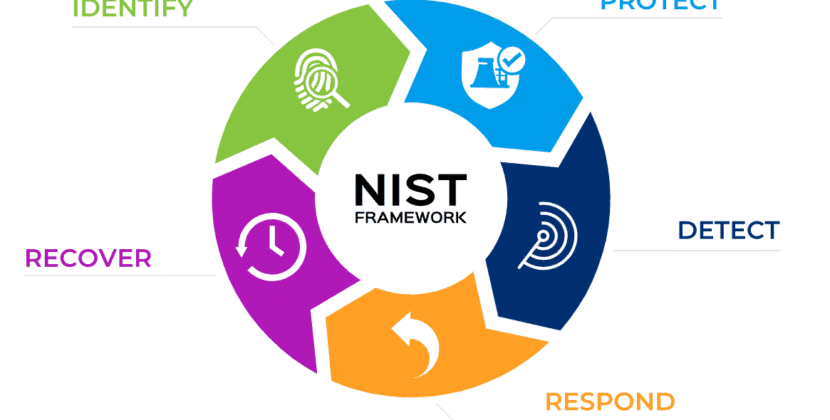
New rules from the National Institute of Standards and Technology mean most enterprise platforms need to adopt identity systems, including RSA and ECC cryptography, which could soon become outdated as post-quantum cryptography standards arrive. The deadline is approaching. Federal agencies expect vendors to present their plans for migrating to new standards before quantum threats become urgent.
For Microsoft, this requires a new review of the authentication layers in Azure Active Directory. Azure security needs more than just minor updates. It needs a major redesign, especially in how credentials are created, verified, and stored across systems.
These changes impact all Azure users, whether they work in healthcare, finance, defense, or any other sector.
Azure security meets NIST compliance mandates.
Compliance is more than just following a checklist. It shapes how systems are designed. The new NIST compliance rules require stronger identity assurance, such as phishing-resistant authentication and hardware-backed credentials. These rules support a zero-trust approach, where no user or device is trusted by default.
Microsoft has begun making these changes, but the new standards raise the bar. Conditional access, multi-factor authentication, and device checks now need to work well with quantum-resistant algorithms. Engineering teams must rethink how to keep systems fast, scalable, and compatible.
At the same time, identity protection is progressing beyond just detecting unusual activity. It is becoming a system that can predict when credentials may be at risk, even in the face of new threats like advanced quantum technology.
The Role Of Cloud Sovereignty In Identity Design.
Compliance requirements now mix with political issues. More governments are seeking cloud sovereignty, meaning data and identity systems must remain within their own countries. For Azure, this means identity-based services operate separately and independently. For example, a European defense contractor cannot use identity checks that pass through US systems. This makes Azure security design more complex because encryption, key management, and authentication must comply with local laws while meeting NIST requirements.
The result is a layered identity system. One layer gives regions control, while another maintains global policies. Keeping both secure without adding risks is a major change for engineers.
Procurement Pressure And The Federal Mandate
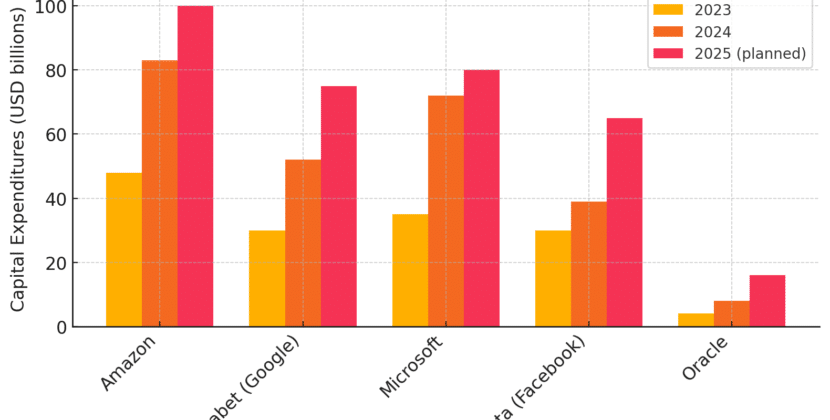
The main driver is that federal procurement contracts now clearly note the impact of NIST post-quantum standards on U.S. government cloud deals. Vendors must demonstrate compliance now and have a plan to adapt their cryptography going forward.
Failure to meet these requirements has direct financial consequences. Losing even one contract could cost billions of dollars. For Microsoft, updating identity systems is essential to remain in the government cloud services market.
This pressure goes beyond federal agencies. State governments and regulated industries often follow federal standards, spreading NIST compliance requirements into the private sector.
Engineering the Shift to Post Quantum Identity
Switching to post-quantum cryptography brings technical challenges beyond simply changing algorithms. Key size increases, modifying how data is saved and sent. Authentication steps must be improved to avoid slowing performance, especially in large organizations.
Microsoft engineers also need to ensure older systems work. Companies cannot switch everything at once. Using both classical and quantum-resistant algorithms together is necessary. This effort adds extra work but keeps systems running smoothly.
At the same time, zero-trust systems require constant checks every time someone tries to access something. The system must verify it with cryptography. This makes efficiency crucial. If not designed well, the system could slow down users.
Identity Production as a Tactical Layer
As threats evolve, identity protection is becoming a key part of strategy, not just a reactive measure. Machine learning now looks for unusual behavior that may indicate credentials are at risk. With new compliance rules, these systems must work with cryptographic protections to build strong, layered defenses.
If an employee’s credentials are exposed, older systems might only reset the password and send alerts. With improved Azure security, the system now adds additional authentication steps, separates sessions, and assesses risk using both behavioral and cryptographic analysis.
This new type of integration highlights a broader trend in NIST compliance: security is built into every part of the system, not added later.
Strategic Consequences for Enterprise Leaders
Executives face a challenging environment. Investing in cloud systems now means committing to and evolving compliance standards. Choosing Azure means adhering to Microsoft’s security and NIST compliance standards.
The benefits are evident: advanced security, compliance with federal standards, and preparedness for future threats. But there are also risks. The costs of moving, integration issues, and potential disruptions could be considered in long-term plans.
Organizations that update identity policies, invest in hardware-backed authentication, and follow zero-trust principles will handle this transition more smoothly.
The combination of compliance, cryptography, and procurement is changing cloud identity in significant ways. How Microsoft responds will determine the future of Azure security and alter the broader enterprise world.
As quantum computing becomes a reality, the need for NIST compliance will increase. Identity systems must keep up, upholding security, ease of use, and regulatory requirements.
Organizations that view this change as an opportunity to improve rather than just a compliance task will be better prepared for a future where trust is always verified and never assumed.
Source: A podcast from Microsoft and Gimlet Creative about making the future happen